The IP (Internet Protocol) is a protocol that uses datagrams to communicate over a packet-switched network. When the IETF defined IPv4, it specified a 32-bit address space [RFC3330], from which people and companies now receive allocations of Internet addresses. A set of addresses have been assigned for special purposes (multicast, private addressing, loopback, etc). The remainder (219,914 blocks, each with 16,777,216 addresses) is being currently allocated by the Internet Assigned Numbers Agency (IANA). IANA regularly delegate address blocks to each of a number of Regional Internet Registries (RIR's). These, in-turn, allocate addresses to operators (e.g. ISPs or large organisations), responsible for assigning addresses to individual users and companies. It was commonly held in the 1990’s that the Internet would run out of IPv4 addresses, and to avoid this, the world would need to transition to use a new version of the IP protocol that permitted a larger address space.
The IETF embarked on a 2.5-year IETF activity callled “IP next generation”, [IPNG], which performed an exhaustive search to identify user requirements, and to assess the good and bad parts of the existing IPv4 protocol. The IPng working group realised that an upgrade also provided a “once in a lifetime” opportunity to fix deficiencies/inefficiencies in IPv4 [RFC1751].
In July 1994, work started on creation of the new protocol, which was published as IPv6 [RFC2460] in 1998.
The key features introduced by IPv6 are:
The network header of the currently deployed IPv4 protocol is 20 bytes (plus options).
IPv6 omits the group of fields in the second 32-byte word of the IPv4 header. A decision was made that IPv6 routers would not support fragmentation within the network, following poor performance for router-based IPv4 fragmentation. IPv6 still supports host-fragmentation and transparent link/tunnel fragmentation (where the packet is reassembled at the next-hop).
The IPv6 header also omits the network checksum. This was removed on the basis that routers were reliable, and that checksum processing incurred an unnecessary overhead in high-speed routers. Instead, IPv6 relies upon the presence of the pseudo-header in the transport checksum to validate that a packet has been delivered to the intended recipient.
The resulting IPv6 base header is 40 bytes. This increase in header size was not accompanied by an increase in complexity; the IPv6 base header is much simpler, comprising just 8 fields. The main reason for the larger size is to accommodate a pair of larger network addresses, increasing the size from 32 to 128 bits.
While the larger address space is a major feature, IPv6 also benefits from a new hierarchical addressing architecture [RFC2491]. Each IPv6 address is formed of a scope, prefix and interface ID. Various types of prefixes are specified: global, link-local, Unique Local (ULA), Multicast, Anycast, or Reserved. A site-local and IPv4-compatible scope were previously defined, but have since been deprecated. Based on this structured approach to addressing, scalable IP routing protocols are being developed.
Each IPv6 unicast address refers to a single interface, rather than the address of a host or router (as in IPv4). All interfaces have at least one Link-Local unicast address, although a single interface may have multiple IPv6 addresses of any type (unicast, anycast, and multicast) and a single or set of unicast addresses may be assigned to multiple physical interfaces if all are treated as one network interface. Any unicast interface address may be used as a node identifier.
An IPv6 address is written as eight sets of four hex characters separated by colons, e.g. 2001:0db8:0001:0035:0bad:beef:0000:cafe. To simplify reading, the leading zeros within each group of four hex digits may be omitted, allowing this to be written as 2001:db8:d:46:bad:beef:0:cafe. Further, one can use ‘::’ once in an address to abbreviate a sequence of consecutive zeros, e.g. 2001:db8:d0:0:0:0:0:1 can be more concisely written as 2001:db8:d0::1.
IPv6 defines both stateful and stateless autoconfiguration. The choice depends upon the expected deployment scenario.
Neighbour Discovery (ND) [RFC 2461] replaces the function of the Address Resolution Protocol in IPv4. It uses IP multicast to determine which hosts and routers are available on-link, or to determine the link address of a specific neighbouring node. Key ND functions are: Router Discovery, Parameter discovery, Redirect, Duplicate Address Detection (DAD) and Neighbour Unreachability Detection (NUD).
The Secure Neighbour Discovery (SEND) protocol [RFC3971] extends ND to address major security concerns associated with ARP.
IPv6 differs from IPv4 in the way the protocol can be extended. IPv4 may be extended by either assigning the (few) reserved bits in the header for new functions, or by including an option field between the network and transport headers. In practice, most IPv4 routers do not efficiently process packets with options, and IPv4 options are therefore normally only used for packets that need to be inspected by all routers along a path.
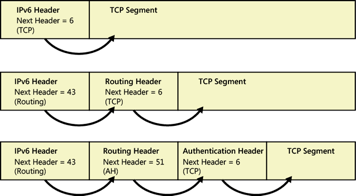
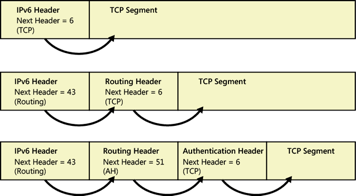
IPv6 Extension Headers, showing a simple TCP payload.
Example showing the routing extension header as well as a TCP payload.
Example showing the routing extension header and an authentication header as well as a TCP payload.
IPv6 uses a modular ‘Next Header’ mechanism, consisting of zero or more extension headers each containing a field identifying the next header. The last header (or base header, if no extensions) identifies the type of the payload. This eases processing and frees IPv6 from a limit to the maximum number of option bytes.
IPv6 refined the QoS model for the Internet, and defined a new header element, the Flow Label, to assist router look-up and to identify sub-flows encrypted using IPsec. Since publishing the base specification of IPv6, IPv4 and IPv6 QoS models have converged. This is not now a major differentiator between the protocols, and the merits of the flow label field remain a matter of controversy among the networking community.
From the outset, security was seen as an important part of the IPv6 stack. The security solution advocated use of IPsec by hosts (required in full IPv6 implementations), however this model did not see widespread use, with IPsec now mostly used in tunnel mode, and additional security commonly implemented above the network layer. IPsec continued to evolve for both IPv4 and IPv6 and is no longer a major differentiator in favour of IPv6.
IPv6 does provide other features that can improve security (e.g. SEND) and its addressing architecture can provide greater resilience to some forms of denial of service attacks.
J. Postel Internet Protocol (STD0005) RFC791
C. Huitema. "IPv6: The New Internet Protocol", Prentice Hall, 1997.
Deering, S. and R. Hinden, "Internet Protocol, Version 6 Specification", RFC 2460, 1998.
Droms, R., Ed., Bound, J., Volz, B., Lemon, T., Perkins, C., and M. Carney, "Dynamic Host Configuration Protocol for IPv6 (DHCPv6)", RFC 3315, 2003.
Arkko, J., Ed., Kempf, J., Zill, B., and P. Nikander, "SEcure Neighbor Discovery (SEND)", RFC 3971, 2005.
Hinden, R. and S. Deering, "IP Version 6 Addressing Architecture", RFC 4291, 2006.
Narten, T., Nordmark, E., Simpson, W., and H. Soliman, "Neighbor Discovery for IP version 6 (IPv6)", RFC 4861, 2007.
Thomson, S., Narten, T., and T. Jinmei, "IPv6 Stateless Address Autoconfiguration", RFC 4862, 2007.